Top Access Control Tips for Global Buyers to Enhance Security
In today's global marketplace, effective Access Control is vital for enhancing security. Experts stress the importance of robust security measures. Dr. Emily Green, a leading authority in the Access Control industry, once stated, "A proactive approach to Access Control is essential to safeguard assets and information."
Access Control involves regulating who can enter designated areas. It is not just about locking doors; it is about creating a secure environment. Organizations must assess their vulnerabilities continuously. Physical security measures often fail without proper policy guidelines.
Many businesses overlook the importance of employee training in Access Control systems. Awareness can significantly reduce human errors. Additionally, technology must evolve to counteract emerging threats. As new methods of intrusion develop, existing solutions may need reevaluation. The challenge lies in striking a balance between accessibility and security.

Top Access Control Tips for Global Buyers to Enhance Security

Access control is pivotal for enhancing security in any organization. Buyers around the globe must prioritize robust systems to protect sensitive information. Effective access control helps in managing who can enter specific areas. It involves both physical and digital barriers. Establishing these measures can deter unauthorized access and potential breaches.
Investing in user training is crucial. Employees must understand the importance of access control policies. They should learn how to recognize security threats. Periodic drills can help reinforce these practices. Moreover, reviewing and updating access lists regularly is essential. Many organizations overlook this step, leading to vulnerabilities.
Technology is advancing rapidly, and it’s key to stay informed. Adopting biometric systems can enhance security. However, users may feel uncomfortable with data collection. Balancing privacy and security is a challenge. Lastly, ongoing assessments of access control effectiveness are vital. An occasional lapse in maintaining protocols can expose weaknesses. Continuous feedback loops from employees can improve strategies.
Understanding the Importance of Access Control in Global Supply Chains
Access control plays a critical role in global supply chains. It dictates who can enter specific areas and handle sensitive materials. With increasing threats, the need for robust access control has never been greater. Companies must recognize that vulnerabilities in security can lead to significant losses. Implementing stringent access rules is not merely a suggestion; it is essential.
Many organizations overlook the importance of regular audits. Without these checks, hidden issues can persist. Training staff on access protocols is crucial. An uninformed employee can inadvertently compromise security. It's not enough to set rules; ongoing education reinforces importance. Regular updates to access privileges based on role changes are also vital.
Embracing technology can enhance access control measures. Biometric systems, for instance, provide a higher level of verification. Yet, these systems aren't foolproof. Dependence on technology without human oversight can create weaknesses. Evaluating the effectiveness of access procedures is a constant process. Perpetual improvement is necessary to maintain security in a dynamic global environment.
Access Control Strategies for Global Supply Chains
Implementing Multi-Factor Authentication in Access Control Systems
Implementing multi-factor authentication (MFA) in access control systems can significantly enhance security for global buyers. Reports have shown that 93% of data breaches could have been prevented with MFA. This statistic underscores the importance of adopting strong security measures, particularly in a world where cyber threats evolve rapidly.
MFA requires users to verify their identity through multiple methods. This can include something they know, like a password, and something they have, like a mobile device. By utilizing these two factors, the likelihood of unauthorized access drops considerably. Yet, challenges remain. Many organizations struggle with user compliance and integration of MFA into existing systems. For example, according to a recent survey, 51% of users find MFA inconvenient, which can lead to a decline in its effectiveness.
Additionally, training staff on proper MFA usage is crucial. Many employees underestimate phishing risks, making them more susceptible to attacks. Research indicates that 72% of organizations report increased phishing attempts during major global events. These trends highlight the need for continuous education and improvement in security practices. Investing in robust access control measures will not only safeguard sensitive data but also build trust with customers and stakeholders alike.
Top Access Control Tips for Global Buyers to Enhance Security - Implementing Multi-Factor Authentication in Access Control Systems
| Tip | Description | Implementation Challenges | Benefits |
|---|---|---|---|
| Use Strong Passwords | Encourage the use of complex passwords that combine letters, numbers, and special characters. | User reluctance to change habits and remember complex passwords. | Increases resilience against brute force attacks. |
| Implement Multi-Factor Authentication | Require additional verification methods like SMS codes or authentication apps. | Integration with existing systems may require additional resources. | Significantly reduces the risk of unauthorized access. |
| Regularly Update Access Controls | Conduct periodic reviews and updates of access permissions and controls. | Requires ongoing investment and attention from security teams. | Ensures that only authorized personnel have access to sensitive information. |
| Educate Employees | Provide training on security best practices, including phishing awareness. | Time and resources required for effective training programs. | Fosters a security-conscious culture and reduces human error. |
| Monitor Access Logs | Regularly review access logs for any suspicious activity. | Can be resource-intensive if not automated. | Helps in early detection of potential security breaches. |
Utilizing Real-Time Analytics for Enhanced Access Security Monitoring
Real-time analytics have emerged as a cornerstone in modern access security systems. They allow security teams to monitor activities instantaneously. This capability enhances the ability to identify and respond to potential threats promptly. With data pouring in from various access points, analyzing it in real time can provide invaluable insights. These insights guide decision-making processes that impact overall security efficacy.
Implementing real-time analytics requires robust infrastructure. Organizations need reliable software and hardware components that integrate seamlessly. Data overload can be a challenge; ineffective filtering may lead to missing critical alerts. Moreover, staff training is essential. Employees must understand how to interpret the data and respond accordingly. Sometimes, even with the best tools, human error can occur in response times. Continuous evaluation of performance is necessary to address these pitfalls.
Furthermore, organizations should collaborate to share best practices. This collective wisdom can improve overall security measures. Regular reviews of access logs, coupled with real-time data, ensure that no abnormal activity goes unnoticed. This comprehensive approach enables businesses to adapt swiftly to evolving security threats. After all, a proactive strategy based on real-time analytics can significantly reduce risks associated with unauthorized access.
Establishing Role-Based Access Control (RBAC) for Improved Accountability
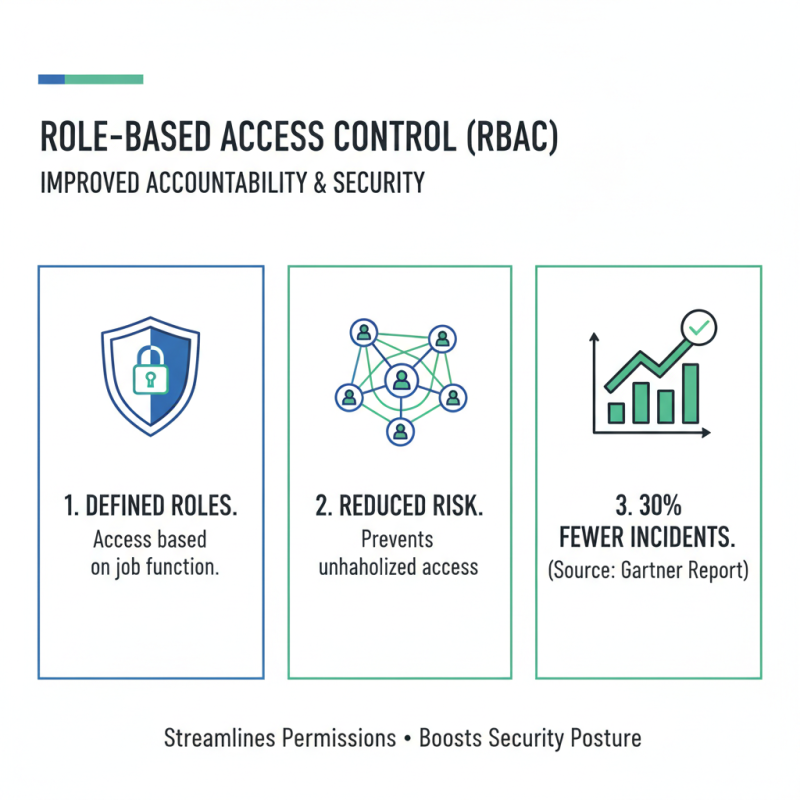
Implementing Role-Based Access Control (RBAC) can significantly enhance security for global organizations. RBAC allocates access rights based on an individual's role within the company, reducing the risk of unauthorized access. According to a recent report from Gartner, organizations that implement RBAC experience a 30% reduction in security incidents. This approach not only improves accountability but also streamlines the management of user permissions.
One effective tip for implementing RBAC is to regularly review and update roles. As organizations evolve, roles may change. Failing to adapt access rights accordingly can lead to vulnerabilities. Additionally, conducting periodic audits helps ensure compliance with internal policies. This practice allows companies to identify any discrepancies and rectify them promptly.
Another key consideration is user training. A study by the Ponemon Institute highlights that up to 70% of security breaches are due to human error. Educating employees about their roles and the importance of access control is essential. Access should never be granted without careful consideration of necessity. This is crucial for maintaining a secure environment while fostering accountability among team members. Each employee must understand their responsibilities in safeguarding organizational information.
Conclusion
Access control is a critical component in securing global supply chains, ensuring that sensitive information and resources are protected from unauthorized access. Implementing effective strategies such as multi-factor authentication can greatly enhance security by requiring multiple forms of verification for users. Additionally, leveraging real-time analytics allows organizations to monitor access patterns and detect potential security threats proactively.
Establishing Role-Based Access Control (RBAC) enhances accountability by ensuring that individuals have access only to the information necessary for their role. Regularly updating access control protocols is also vital in mitigating security breaches and adapting to emerging threats. By prioritizing these access control measures, global buyers can significantly bolster their security posture and protect their assets in an increasingly interconnected world.
Related Posts
-

Digital Innovations in Best Access Control Security Solutions
-

Ultimate Guide to Selecting the Best Access Control Panel for Your Security Needs
-

Top Access Control Software Solutions for Your Business Needs?
-

2026 Best Access Systems for Enhanced Security and Efficiency Options?
-

How to Choose the Best Access Control Solutions for Your Business?
-

How to Choose the Best Access Control Software for Your Business?
- • HighpowerOne Touchscreen Controller • HighpowerOne Mobile Credential App
- Highpower Management System
- • Pushplate 100 PNZ
- • Pushplate 110 PNZ
- • Pushplate 120/140 PNZ
- • Pushplate 130/150 PNZ
- • Pushplate 200 PNZ
- • Pushplate 100
- • Pushplate 110
- • Pushplate 120/140
- • Pushplate 130/150
- • Pushplate 200
Mechanical Timers
Proximity ID Access Cards and Fobs
Proximity Card Readers
- • Proximity Reader P-300
- • Proximity Reader P-400
- • Proximity Reader P-500
- • Proximity Reader P-620
- • Proximity Reader P-640
- • Proximity Reader P-710
- • Proximity Reader P-900
- • Ranger Proximity Readers
- • Ranger Controls
- • Sure-Fi Wireless Interfaces
Smart Series JX Readers
Electromagnetic Locks
Highpower Power Supplies
• H505
• H512
Security Products Summary
